IFSEC Distributor Network - Ask the Security Experts
As part of the UK's leading security expo - IFSEC 2023 at ExCel London, HowToAV brought together a panel of experts from some of the UK's leading security distributors to answer your questions on latest technology, trends and installation challenges from the world of video surveillance, access control and smart home technology.
00:34 Meet the experts from our IFSEC Distributor Network security panel:
- Kevin Sherwood, CIE-Group
- David Davies, DVS
- Camilla Kirkham, Nimans
- Carl Spencer, Oprema
- Daniel Frith, DTS Solutions
Presenter:
01:56 What is the role of a Value-Added Distributor in security technology?
We discuss how the model of the trade distributor has significantly changed in recent years, from simple 'box shifting' to a service-driven business model to provide customers with education and pre- / post-sales support as part of the product offering.
A value-added distributor (VAD) sits between technology manufacturers and end customers. Its primary role is to enhance the value of the products it distributes by providing additional services and expertise.
Unlike traditional distributors which primarily handle logistics and supply chain management, value-added distributors such as CIE-Group go beyond simple product delivery. They add value to the distribution process by offering services such as:
- Technical Support
- Pre-Sales Consultation
- Training and Education
- Customization and Integration
- Marketing and Sales Support
- Value-Added Services such as managed services or specialised consulting
05:37 Is AI technology a benefit or a threat to the security industry?
It's important to note that while AI (artificial intelligence) brings a variety of benefits to security hardware and technology, it also presents challenges. Ethical considerations, privacy concerns, and the potential for malicious attacks on surveillance and access control systems are some of the issues that need to be addressed as AI continues to evolve in the security industry.
How can artificial intelligence (AI) support security hardware and technology?
-
Threat Detection:
AI-powered security systems can analyse huge amounts of data in real-time, enabling them to identify patterns and anomalies that may indicate security threats.
-
Video Surveillance:
AI enhances video surveillance systems by enabling advanced video analytics. AI algorithms can automatically analyse video feeds, identify objects or individuals of interest, and trigger automated alerts for potential security breaches or suspicious activities. Facial recognition technology, powered by AI, can help in identifying and tracking individuals in real-time, aiding in surveillance tracking.
-
Access Control:
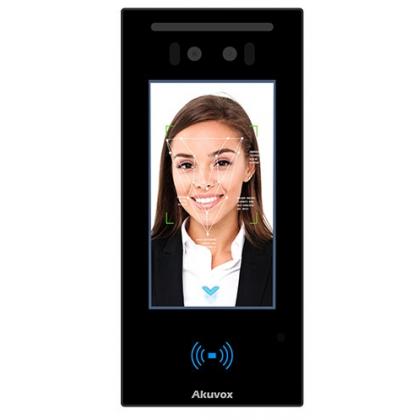
AI can improve access control systems by incorporating biometric authentication methods such as facial recognition or fingerprint scanning. These systems can accurately verify the identity of individuals and grant access based on pre-defined rules, enhancing security and preventing unauthorised access.
-
Security Automation:
AI can automate security processes, reducing the need for manual intervention and enabling faster response times. Automated systems can identify and respond to security incidents, initiate appropriate actions, and generate alerts for security personnel to investigate further. This improves operational efficiency and reduces the risk of human error.
-
Predictive Analysis:
AI-powered security systems can analyse historical data and use predictive analytics to anticipate potential security risks. By identifying patterns and trends, AI algorithms can provide proactive insights and recommendations, allowing organisations to implement preventive measures and stay ahead of emerging threats.
08:30 How can security technology support the requirements Martyn's Law?
Martyn's Law is a new legislation whihc will mandate responsible parties for specific venues to assess the risk of terrorism and implement suitable measures to mitigate the risk.
This new lehislation, set to become law in early 2024, aims to ensure that individuals are adequately prepared, equipped to respond, and knowledgeable about appropriate actions during an attack. Enhanced security systems, staff training and streamlined procedures will contribute to better protection for the public.
The implementation of this legislation is a direct response to the Manchester Arena Inquiry, which recommended the introduction of laws to enhance the safety and security of public venues.
According to the legislation, standard tier sites (with a capacity ranging from 100 to 799) must utilise an evaluation template to enhance their readiness in quickly responding to terrorist attacks and preserving lives.
10:29 How do manufacturers respond to changes in security legislation?
11:10 How has the chipset shortage affected supply and new product development?
13:50 Which is the best contactless access control technology?
The panel discuss the various contactless authenticiation methods for door unlocking and access control and which technology provides the best solution to various security applications.
Contactless authentication methods include:
- RFID (using either a keyfob or card)
- Bluetooth/BLE (via smartphone)
- NFC (via smartphone)
- Biometrics (such as face recognition)
- QR Code scanning (temporary 'key' generation for limited-time or single-use access)
CLICK HERE to watch our video and read our detailed blog on Contactless Accesss Control.
19:05 Is installer adoption of IP systems and working with IT managers still a challenge?
21:52 What tips for installing devices in harsh weather environments?
24:26 Are cloud-based systems the future of security?
Find out more about Access Control and Door Intercoms:
-
Protecting Public Spaces: An In-Depth Look at Martyn's Law
-
CIE adds Carson 24/7 remote concierge service to IP Intercoms
-
Tips for Access Control & Door Intercom system design
-
What is Access Control?
-
What is a Contactless Pathway?
-
What is Bluetooth BLE Access Control?
-
Keyless Door Entry Systems
Talk to the CIE team about Access Control and Door Entry SystemsIf you would like to discuss your next Access Control or Door Intercom system, please call the CIE sales team on T. 0115 9770075 or email [email protected].
|